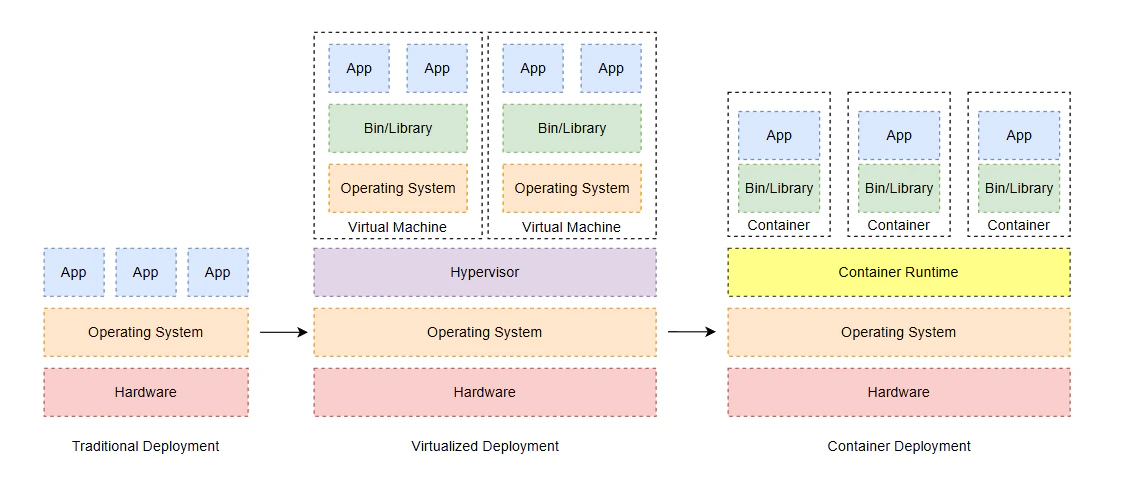
Before we dive into the details of Kubernetes, it’s useful to understand the evolution of deployment strategies over time. This comparison will help you see how Kubernetes fits into the broader context of application deployment and why it has become such a popular choice for modern applications.
| Aspect | Traditional Deployment (Bare-Metal) | Virtualized Deployment (VMs) | Container Deployment |
|---|
| Definition | Applications run directly on physical servers with the host OS. | Applications run inside virtual machines (VMs) on a hypervisor, each with its own guest OS. | Applications run in lightweight, isolated containers sharing the host OS kernel. |
| Resource Utilization | Low overhead; direct hardware access. | Moderate; VMs include full OS overhead. | High efficiency; minimal overhead per container. |
| Isolation | Limited; apps share the same OS, risking interference. | Strong; each VM is fully isolated with its own OS. | Good; containers isolate processes but share the kernel. |
| Portability | Low; tied to specific hardware/OS. | Moderate; VMs can be moved but include OS baggage. | High; containers are OS-agnostic and portable across environments. |
| Scalability | Manual; scaling requires new hardware. | Better; VMs can be cloned/spun up quickly. | Excellent; containers start/stop in seconds, ideal for microservices. |
| Management Overhead | High; manual provisioning, patching, and maintenance. | Moderate; hypervisor management, but still OS-level tasks. | Low; orchestration tools (e.g., Kubernetes) automate scaling and updates. |
| Startup Time | Slow; full OS boot required. | Moderate; VM boot takes time. | Fast; containers start in milliseconds. |
| Security | Vulnerable to OS-level attacks; no built-in isolation. | Improved; VM isolation prevents lateral movement. | Strong; container isolation plus tools like seccomp/AppArmor. |
| Cost | High; dedicated hardware per app. | Moderate; shared hardware but VM licensing costs. | Low; efficient resource use, open-source tools. |
| Use Cases | Legacy apps, monolithic systems. | Mixed workloads, development/testing environments. | Cloud-native apps, microservices, CI/CD pipelines. |
| Examples | Direct installation on servers (e.g., Apache on Linux). | VMware, Hyper-V VMs. | Docker, Kubernetes pods. |